When working with SIP traffic captures for debugging, analysis, or sharing with colleagues, you often need to protect sensitive information like phone numbers, domains, and IP addresses. However, you still want to maintain the ability to follow call flows and understand the signaling behavior. This is where anonymization becomes crucial.
I’ve created a simple Python tool called anonymize_sip that helps you anonymize SIP traffic in PCAP/PCAPNG files while preserving the structure and relationships in your captures.
Why Anonymize SIP Captures?
There are several scenarios where you need to anonymize SIP traffic:
- Sharing captures for troubleshooting: When you need to share a PCAP file with a vendor or colleague, you want to protect customer privacy
- Documentation and training: Creating examples or training materials without exposing real phone numbers or network infrastructure
- Compliance: Meeting privacy requirements when storing or analyzing call data
- Testing: Creating sanitized test data from production captures
The challenge is that simple find-and-replace doesn’t work well because:
- The same phone number appears in multiple headers (From, To, Contact, P-Asserted-Identity, etc.)
- You need consistent mapping so
+11234567890in one packet maps to the same anonymized value in all packets - Call-IDs need to be anonymized but still allow you to correlate messages within the same dialog
- Phone numbers can appear in different formats (
+11234567890,11234567890,1234567890) but should map to the same anonymized value
Features
The tool provides several key features:
Consistent Anonymization
The same original value always maps to the same anonymized value throughout the entire capture. This means if +11234567890 appears in the From header of an INVITE and later in the Contact header of a 200 OK, both will be replaced with the same anonymized identifier (e.g., user_001).
Phone Number Normalization
Phone numbers are normalized before anonymization, so +11234567890, 11234567890, and 1234567890 all map to the same anonymized value. This is especially important for North American numbers where the country code +1 might be included or omitted.
Comprehensive Header Support
The tool anonymizes all common SIP headers that contain user identities:
- From, To, Contact
- P-Asserted-Identity, Remote-Party-ID
- Diversion, P-Called-Party-ID
- History-Info, P-Charge-Info
Call-ID Correlation
Call-IDs are anonymized consistently, so you can still follow a call flow from INVITE through BYE, even though the Call-ID itself is anonymized.
Optional IP Anonymization
You can optionally anonymize IP addresses at both the packet layer and within SIP/SDP content. When enabled, it anonymizes:
- Packet source and destination IPs
- IPs in Via, Route, Record-Route, Path headers
- IPs in SDP
c=ando=lines
Memory Efficient
The tool streams packets instead of loading the entire file into memory, making it suitable for large capture files.
Usage
Basic usage is straightforward:
|
|
To also anonymize IP addresses:
|
|
To see the mapping table after processing:
|
|
What Gets Anonymized
Always Anonymized
| Field | Example Before | Example After |
|---|---|---|
| From header | sip:+11234567890@example1.com |
sip:user_001@domain_001.example |
| To header | sip:+10987654321@example2.com |
sip:user_002@domain_002.example |
| Contact | sip:+11234567890@10.0.0.1:5060 |
sip:user_001@domain_003.example |
| P-Asserted-Identity | tel:+11234567890 |
tel:user_001 |
| Call-ID | abc123@host.example.com |
call-id-0001@anonymous.example |
| Request-URI | INVITE sip:+10987654321@... |
INVITE sip:user_002@... |
With --anonymize-ips
| Field | Example Before | Example After |
|---|---|---|
| Packet source IP | 192.168.1.100 |
10.0.0.1 |
| Packet dest IP | 192.168.1.200 |
10.0.0.2 |
| Via header | Via: SIP/2.0/UDP 192.168.1.100:5060 |
Via: SIP/2.0/UDP 10.0.0.1:5060 |
| SDP c= line | c=IN IP4 192.168.1.100 |
c=IN IP4 10.0.0.1 |
| SDP o= line | o=- 123 456 IN IP4 192.168.1.100 |
o=- 123 456 IN IP4 10.0.0.1 |
How It Works
The tool uses Scapy to read and write PCAP files. It processes each packet by:
- Identifying SIP packets: Quick signature check for SIP indicators (SIP/2.0, INVITE, REGISTER, etc.)
- Extracting SIP content: Decoding the UDP/TCP payload as UTF-8
- Anonymizing SIP headers: Using regex patterns to find and replace URIs, phone numbers, and Call-IDs
- Maintaining mappings: Keeping dictionaries that map original values to anonymized values
- Reconstructing packets: Rebuilding the packet with anonymized content and recalculating checksums
The anonymization maintains consistency by using the same mapping dictionaries throughout the entire file processing.
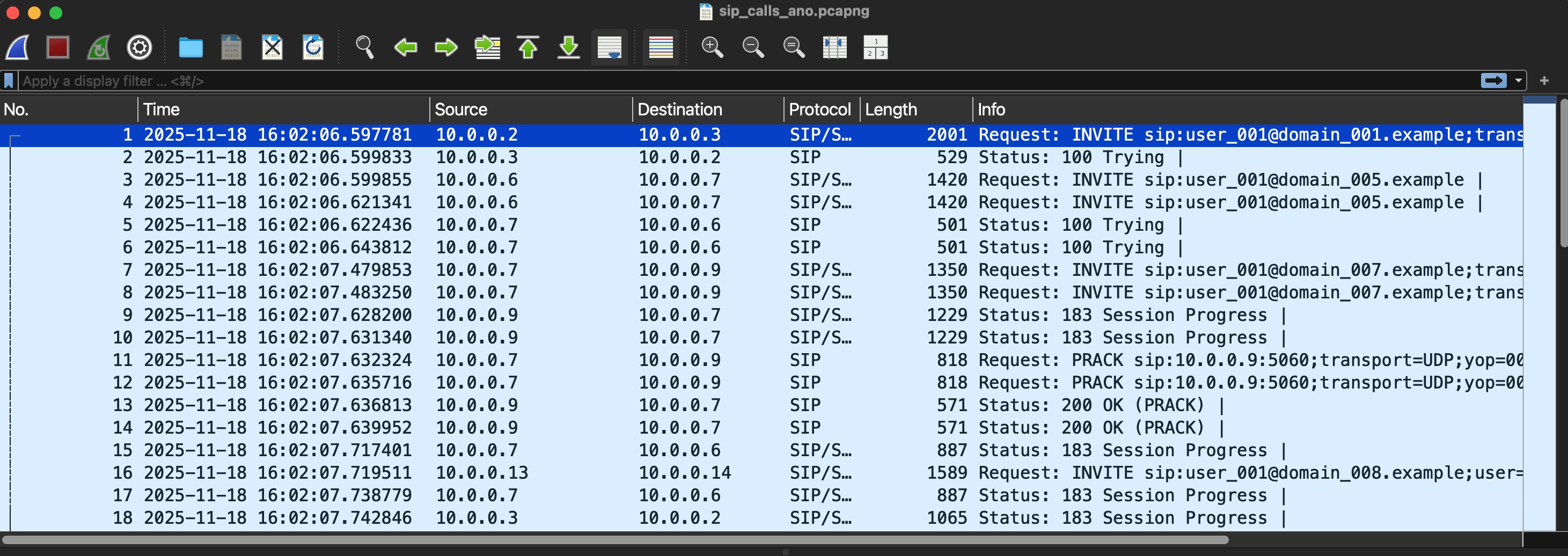
Example Output
When you run the tool with --show-mapping, you get a summary of all anonymizations:
$ python anonymize_sip.py --anonymize-ips --show-mapping capture.pcap anon.pcap
Processing: capture.pcap
IP anonymization: enabled
Processed 1500 packets...
Done! Processed 1523 packets.
Anonymized: 5 users, 3 domains, 12 Call-IDs, 8 IPv4
Output: anon.pcap
============================================================
ANONYMIZATION MAPPING SUMMARY
============================================================
User Mappings (phone numbers normalized):
user_001 <- 1234567890
user_002 <- 0987654321
user_003 <- 1112223333
Domain Mappings:
domain_001.example <- example1.com
domain_002.example <- example2.com
domain_003.example <- ims.mnc000.mcc000.3gppnetwork.org
IPv4 Mappings:
10.0.0.1 <- 192.168.1.100
10.0.0.2 <- 192.168.1.200
10.0.0.3 <- 10.10.44.131
Call-ID Mappings: 12 unique Call-IDs
============================================================
Extending the Tool
The tool is designed to be easily extensible. You can add support for additional SIP headers by modifying the IDENTITY_HEADERS or IP_HEADERS lists in the code:
|
|
Important Notes
- The output file has recalculated checksums, so it’s a valid PCAP file
- Ports are preserved (not anonymized)
- The mapping is deterministic within a single run but changes between runs
- Keep the
--show-mappingoutput private if you need to correlate back to original values - The tool only processes SIP packets; other traffic passes through unchanged
Installation
The tool requires only Scapy:
|
|
You can find the source code and more details in the anonymize_sip repository.
This tool has been useful for me when sharing captures for troubleshooting or creating documentation. If you find it helpful or have suggestions for improvements, feel free to contribute!
Take care and stay safe! ;)