 Caption: Photo courtesy of John Downer Productions
Caption: Photo courtesy of John Downer Productions
Lawful Interception (LI) standard play a crucial role in enabling lawful interception activities by authorized entities for security and intelligence purposes. These protocols allow the interception and monitoring of communication services while adhering to legal requirements. If you’re involved in IMS/mobile core or other telephony networks development, or communication analysis and security, you’ll find a dissector besides Wireshark be an invaluable addition to your toolkit. In this blog post, I’ll introduce you to x2x3PduDissector, a powerful Lua-based Wireshark dissector for analyzing LI (X2/X3 PDU Format) packets.
What is x2x3PduDissector?
x2x3PduDissector is an open-source project available on GitHub that provides a Wireshark Lua script for dissecting LI packets. The script is designed to decode various fields within the X2/X3 PDU Format, making it easier for network analysts to understand and interpret captured traffic related to this protocol.
Key Features:
- It is based on ETSI TS 103 221-2 V1.4.1 - April 2021
0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Version | PDU Type +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Header Length +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Payload Length +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Payload Format | Payload Direction +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | | | XID | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Correlation ID | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Conditional Attribute Fields (Variable Length) +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Payload (Variable Length) +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
-
Version, PDU Type, Header Length, Payload Length, Payload Format, Payload Direction, XID (UUID), Correlation ID, and Conditional Attributes are all decoded for thorough analysis.
-
Payload interpretation for RTP and SIP messages is included.
-
Conditional attributes are dissected as Type-Length-Value (TLV) structures.
-
The script enhances the analysis of LI packets by providing a clear representation of the protocol’s fields and their semantic meanings.
Usage:
To use x2x3PduDissector, follow these steps:
-
Clone or download the repository from GitHub: https://github.com/hyavari/x2x3PduDissector
-
Place the Lua script in Wireshark’s Plugins directory or load it manually through the “Tools > Lua > Evaluate” menu.
-
Once loaded, the script will automatically dissect packets using the “X2X3” protocol.
Example Output:
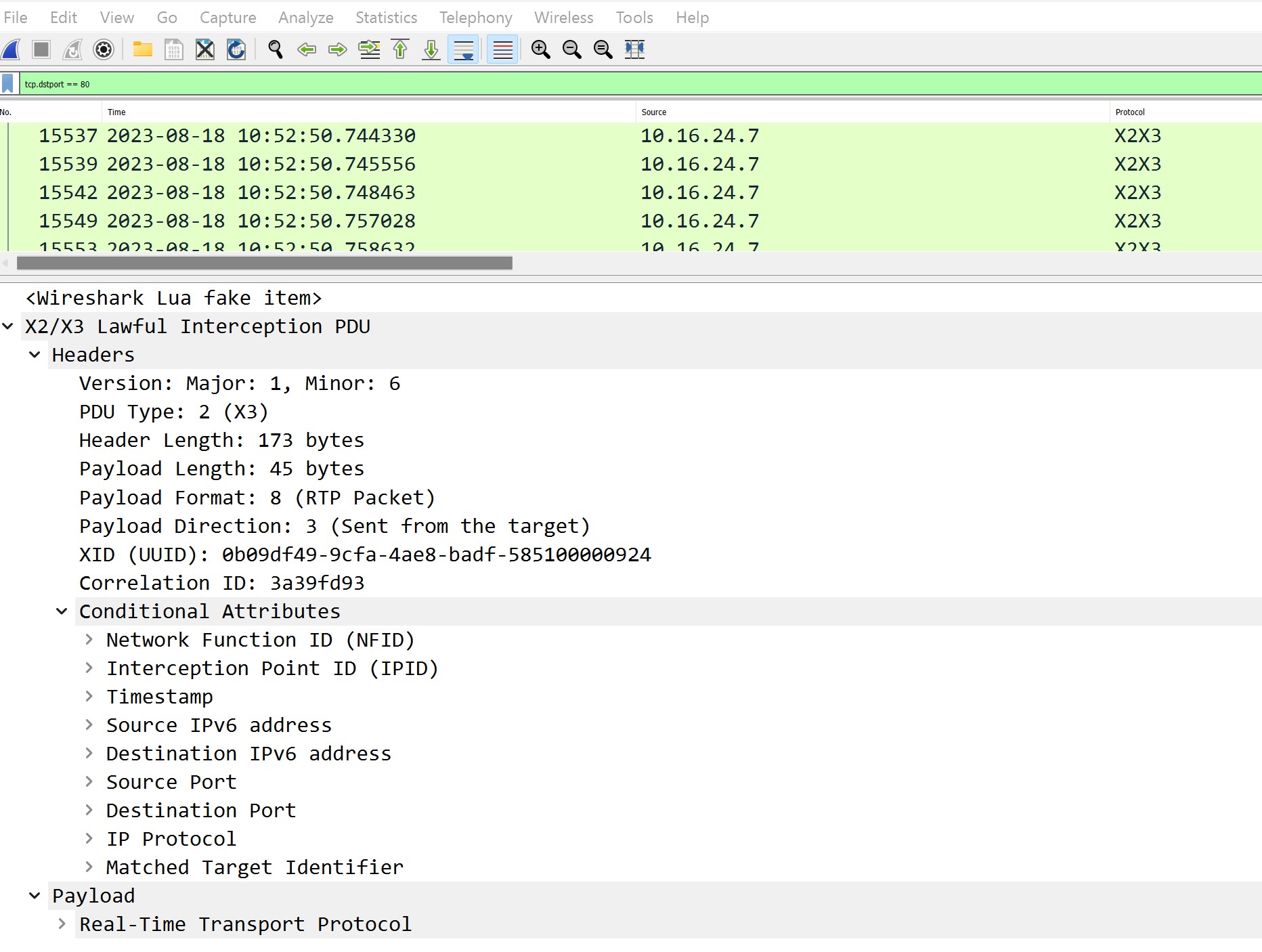
Once the script is applied in Wireshark, you’ll see a detailed breakdown of each packet’s fields and values. This breakdown includes information such as the PDU type, payload format, XID (UUID), and more. Conditional attributes are dissected to provide a deeper insight into the packet’s content.
Contributions and Enhancements:
x2x3PduDissector is an open-source project, which means you can contribute to its development and enhancement. If you encounter any issues or want to improve its functionality, consider submitting pull requests or reporting issues on the project’s GitHub repository.
Notes:
-
LI (X1/X2/X3) is standard, but most of the vendors do not follow the standards when they are using their proprietary software or implementation. So do Not be upset if this dissector can’t help you :)
-
I also implement a simple X2/X3 PDU decode in node.js. You can find it here: https://github.com/hyavari/x2x3PduDecoder
-
These repos are for half-day work and I will update them if I find any issues.
-
Always there is place for improvement, so please do not hesitate to contribute them.
-
Do not forget to sarring these projects :))